When you are installing Microsoft SQL Server Management Studio Express on Windows Vista or Windows 7, you may receive this error message:
The installer has encountered an unexpected error installing this package. This may indicate a problem with this package. The error code is 29506.
This error message relates with permission issue (UAC) on Windows Vista and Windows 7. To solve this problem, you have to re-run the installer again using elevated command prompt by run the command prompt as administrator and execute the installer in there. If you are using 64-bit Windows, you should use the command prompt at C:\Windows\SysWOW64\cmd.exe instead. Otherwise, you can use the command prompt at C:\Windows\System32\cmd.exe.
- 32-bit Windows : Run elevated command prompt by right-click on Command Prompt in Start -> All Programs -> Accessories -> Command Prompt and select Run as administrator.

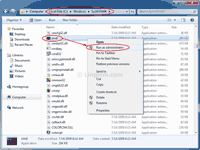
- 64-bit Windows: Run the command prompt in C:\Windows\SysWOW64. Right-click on cmd.exe and select Run as administrator.
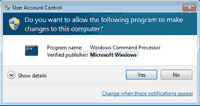
- On User Account Control, click Yes.
- On Command Prompt (both 32-bit and 64-bit Windows), change path to directory where the installer file is and execute the file. By default, the file name for 32-bit version is SQLServer2005_SSMSEE.msi and 64-bit version isSQLServer2005_SSMSEE_x64.msi.
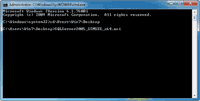
- On Setup Wizard, follow the instruction as usual. There won’t be the error message this time.